Identity attacks
Identity-based threats now account for more than half of our total confirmed threats, following an 850 percent increase in identity threat detections year over year.
Despite continued advancements in authentication controls, including centralized identity and access management (IAM) providers and the widespread adoption of multi-factor authentication (MFA), identity attacks continued to dominate the threat landscape in 2025.
As identity has expanded to replace traditional network boundaries in the shift to cloud-based environments, adversaries have recognized that compromising valid user accounts is significantly more effective than exploiting technical vulnerabilities. This evolution reflects a continuing change in enterprise architecture in which organizations are increasingly distributing resources across numerous platforms, devices, SaaS applications, and hybrid workforces.
With the success of past attacks and the continued adoption of identity federation, this trend is likely to continue into 2026 and beyond.
Identity threats increased by 850 percent from 2024, accounting for 53 percent of overall detection volume in 2025.
Identity attacks in 2025
It was a busy year for identity attacks, and Red Canary saw it all: From the proliferation of device code phishing, to sophisticated adversary-in-the-middle (AitM) attacks, to tried-and-true social engineering techniques. Credential harvesting was a major theme as well, with multiple high-profile attacks leveraging common security tools to discover and exploit valid credentials.
Identity detections in 2025
As we continue to develop and deploy AI agents throughout our platform integrations, we are enriching context and providing data correlation that empowers our detection engineers to identify threats faster. Last year we detailed how endpoint threats make up the bulk of what we detect due to the variation in customer adoption, and this year we saw identity detections overtake endpoint detections by a significant margin. Identity threats increased by 850 percent from 2024, accounting for 53 percent of overall detection volume in 2025.
Methods and madness
While not an exhaustive list, we routinely observe adversaries attempting the following techniques to compromise identities.
Infostealers
Infostealers have evolved into a sophisticated credential harvesting ecosystem, with malware-as-a-service (MaaS) families like Atomic Stealer, Odyssey Stealer, and Rhadamanthys systematically exfiltrating passwords, session tokens, access keys, and other credentials that can provide access without triggering additional authentication requirements. Competition in the commoditization of infostealer malware is likely to continue in 2026.
(In)direct credential exposure
Adversaries are increasingly using legitimate security tools to discover and validate credentials from victim environments. This not only includes endpoints, but communication platforms, knowledge bases, and source code repositories.
Distributed, cloud-based workloads have made authenticating to numerous public-facing services the norm, and adversaries routinely find plaintext secrets in environment variables, CI/CD pipeline, and container definition files, using them to pivot to other services and platforms. These non-human identities are commonly excluded from MFA requirements and are oftentimes not subject to additional contextual controls.
Recent major attacks involving credential harvesting include Sha1-Hulud: The Second Coming and the September 2025 breach of Red Hat Consulting.
Device code phishing
We predicted back in 2022 that device code phishing would likely have a real impact in the future and 2025 was a banner year. Device code phishing abuses the legitimate OAuth device authorization grant flow, which is intended for devices with limited input capabilities, such as televisions. Adversaries register their own third-party applications, request device codes tied to those applications, and trick victims into entering the codes on legitimate login pages to grant access to the malicious application.
Consent phishing
Consent phishing also takes advantage of OAuth authorization flows by presenting victims with consent requests for applications that have been registered with legitimate providers, such as Microsoft Entra ID, but that are controlled by adversaries. These third-party applications typically masquerade as trusted services by using similar naming conventions and validated domains that closely resemble legitimate publishers.
Brute force
Password-spraying attacks work by testing common or easily guessed passwords against many accounts simultaneously, deliberately staying below account lockout thresholds to avoid detection while maximizing the chance of finding weak credentials.
Credential-stuffing attacks exploit widespread password reuse by automatically testing username and password combinations stolen from previous data breaches.
Adversaries are increasingly combining password spraying and credential-stuffing techniques, leveraging massive databases of breached credentials from infostealers and data leaks to inform their target and password lists, making these attacks more effective against organizations with weak password policies and relaxed MFA requirements.
MFA bypass
Token theft
Token theft remains a favored attack method for adversaries due to the continued proliferation of browser exploits and commoditization of infostealer malware. Once obtained, stolen tokens allow adversaries post-MFA access to all of the resources the victim is authenticated to until the session either expires or is revoked. Learn more on the Steal Application Access Token technique page.
Adversary-in-the-middle (AitM) phishing kits, a component of the broader phishing-as-a-service ecosystem, allow adversaries to deploy a reverse proxy between victims and legitimate authentication services. As victims interact with spoofed versions of login pages, requests and responses flow through these proxies, where adversaries can collect authenticated session tokens that are returned from the legitimate service.
MFA fatigue
Also referred to as “push bombing” or “flooding,” MFA fatigue attacks involve an adversary with legitimate credentials rapidly triggering MFA push notification requests to frustrate the user into accepting the request and granting access.
All roads don’t have to lead to identity compromise. Start off by evaluating the tools you already have and understanding the capabilities offered by your existing identity provider and licensing. Reducing complexity is the key to understanding your attack surface and allowing faster, more effective detection and response.
Mitigation
MFA
Adversaries have continually proven their ability to circumvent weak MFA methods including SMS, voice, and email notifications. Disabling these methods in favor of phishing-resistant methods such as hardware security keys, passkeys, and device-bound biometrics will help mitigate common attacks like phishing and one-time password (OTP) interception. If mobile authenticator applications are allowed, ensure that number matching is required to reduce the efficacy of MFA fatigue attacks.
Abuse of MFA device registration by adversaries with legitimate user credentials has also become rampant, so we recommend using contextual controls, such as requiring network origination from a trusted location.
Contextual controls
Contextual controls, such as Microsoft Entra ID’s Conditional Access and Google Workspace’s Context-Aware Access, provide granular, policy-based access controls. To maximize their effectiveness and reduce common coverage gaps, focus on deploying a small number of baseline policies to enforce core security controls such as MFA and device requirements. Defining policy inclusions and exclusions by groups instead of individual users will also help reduce policy sprawl and management complexity.
Contextual controls are especially important for non-human identities and can add mitigating controls such as network origination requirements.
Finally, if your license includes it, implement risk-based policies such as sign-in and user-risk.
Test your contextual controls regularly for policy and assignment gaps. Many identity providers provide native tools that can evaluate policy enforcement based on atomic-level conditions.
Session duration
Limiting the duration of sessions reduces the window of opportunity for adversaries who have successfully stolen tokens by requiring periodic reauthentication. Session duration defaults are often set to allow long-lived authentication, with some up to 90 days.
Credential discovery
With the increase in adversarial use of secrets discovery tools, beat them to it. Open source tools such as TruffleHog and Gitleaks can be used to locate common secrets patterns across a multitude of platforms including local file systems, source code repositories, and collaboration tools.
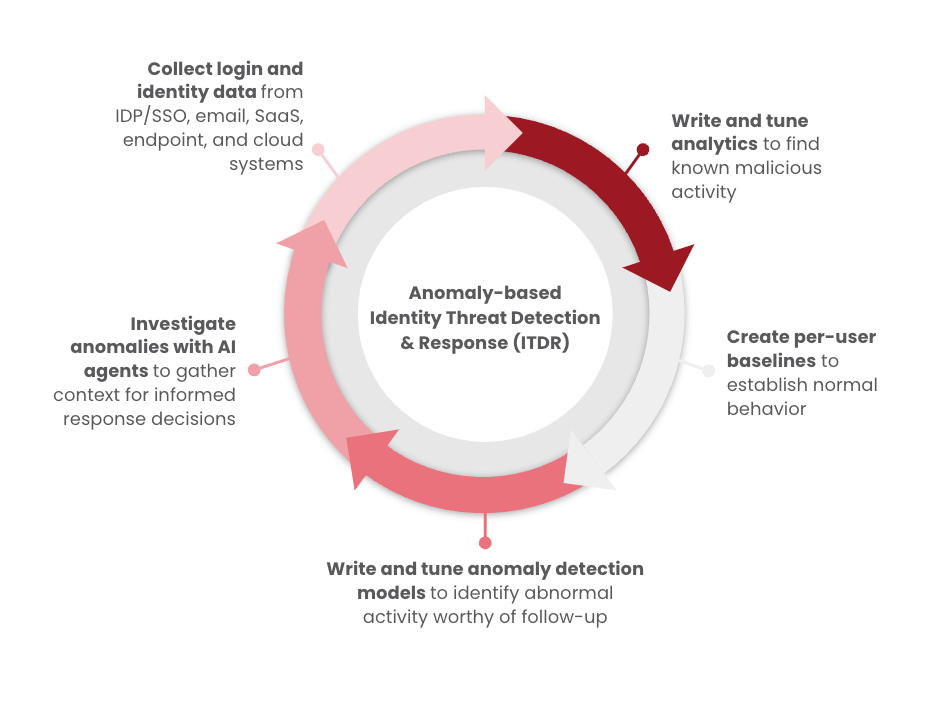
Many identity providers generate native alerts for what they consider to be suspicious or malicious login attempts; however, these alerts can be significant in number, difficult to triage and investigate, and can often overwhelm security teams with noise. Identity threat detection and response (ITDR) solutions collect telemetry and alerts directly from identity providers and allow security teams or third-party service providers to build real-time, custom detection rules.
While far from comprehensive, the following events and user patterns are helpful for conducting investigations and building custom detection rules:
Failed authentication patterns
- High volume of failed attempts across multiple user accounts
- Consistent timing intervals
- Anomalous velocity, including attempt rates over time
Successful authentication patterns
- Anomalous MFA notification volume and velocity
- Anomalous number of MFA notification denials
- OAuth consent grants for unknown applications, unverified publishers, and recent registrations
Source IP characteristics
- Anomalous network origination including high-risk regions
- Impossible travel scenarios including session concurrency across different regions
- Anomalous VPN, ISP, or ASN
- Connection from known Tor exit nodes
- Low IP reputation scores
- IP characteristic variations against the same user account
- Similar IP characteristics across multiple user accounts
User agent analysis
- User agents indicating automation or security testing tools
- Outdated or unusual browser versions used consistently across multiple user accounts
- Browser/device mismatches
- Missing or malformed user agent strings
Start testing your defenses against identity threats using Atomic Red Team—an open source testing framework of small, highly portable detection tests mapped to MITRE ATT&CK.
Getting started
Atomic Red Team has a variety of tests that security teams can run to validate and improve their defense controls for detecting and preventing identity abuse. The following five are a great starting point. Run them and then examine whether or not you managed to detect, prevent, or observe the suspicious activity.
- Password Spraying Azure/O365 accounts
- Password Spray Azure/O365 account with a single password
- AWS account password spraying
- AzureAD Application Hijacking – Service Principal
- AzureAD Application Hijacking – App Registration
Review and repeat
Now that you have executed one or several common tests and checked for the expected results, it’s useful to answer some immediate questions:
- Were any of your actions detected?
- Were any of your actions blocked or prevented?
- Were your actions visible in logs or other defensive telemetry?
Repeat this process, performing additional tests related to this technique. You can also create and contribute tests of your own.