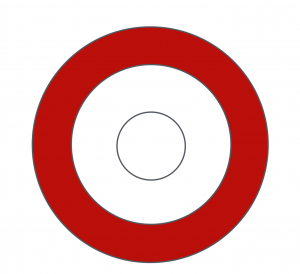
“Threat Intelligence” is the latest security concept to undergo aggressive cyber-buzzwordification (this is a real word). This is common in the information security industry, and follows a very predictable cycle:
Discovery
A real and valuable concept starts to take hold, and high-functioning security teams leverage the concept with great success.
Socialization
In a genuine interest to improve the security game, the idea is socialized and discussed heavily within the security community. Other high-functioning teams start to adopt it and build interest in the concept.
Marketization
Vendors smell revenue and every single company suddenly has an offering that provides the concept. Many will state, “We’ve been doing this concept for years but it’s called ProprietaryTerm™!” More than 90% of the booth banners at major security conferences feature the concept.
Misguided implementation
Executives, often with no knowledge of the concept’s use case, take the bait—hook, line, and sinker. If you’re lucky, the execs ask the security team how they are implementing the concept, or when it will be used in the environment. If you’re less lucky, the exec buys some service or product that claims to provide the concept and tells the security team it’s a done deal.
Failure
The security team attempts to implement the concept, but the vendor’s approach is too generic, not designed for the organizational policy, and/or is otherwise not tuned to the team’s and organization’s real-world needs.
Improvement
The security team starts to seek out new ways to have a meaningful impact to their operations.
GO TO STEP 1
Given that this is a reality, we’ll look at the buzzwordification of Threat Intelligence in an attempt to discern the truth from the hype.
The Real Definition of Threat Intelligence:
threat intelligence:
(noun)
the collection, classification, and exploitation of knowledge about adversaries, usually with the intent of turning that Intelligence into actionable steps to find, limit, stop, and/or remove the attackers from the victim’s environment.
As a core concept, threat intelligence is an invaluable component to a broader information security program.
The Perceived Definition of Threat Intelligence:
Unfortunately, the deep and complex topic of threat intelligence has been diluted to supposedly simple, turnkey solutions that often don’t have meaningful impact for the organization using it.
When asked if they are using threat intel, many security personnel are quick to reply “Oh yeah, we bought a feed service” or something similar. This behavior essentially mirrors the initial IDS craze of the late 1990s (and, unfortunately, still today for some organizations), in which an “IDS program” consisted of turning on all available signatures and trying to wade through the thousands of alerts per day.
Another aspect of threat intelligence missed by organizations new to the concept is the different levels used for classifying each source. Threat intelligence can be strategic, operational, or tactical. These different levels generally suggest the audience, use case, and longevity for each.
The three levels threat intelligence include:
1: Strategic Threat Intelligence
Strategic threat intelligence is extremely broad and often does not even lend itself to technical indicators. For example, an organization that performs banking functions might use a statement such as “our industry is generally attacked by organized crime actors, while our customers are often targeted by opportunistic lower-level criminal actors.” While there are no IP addresses, malware hash values, or other specifics associated with this intelligence, it still broadly characterizes the organization’s risk profile and the types of actors they are most likely to face. Strategic intelligence is typically valid for a longer period of time than other levels.
2: Operational Threat Intelligence
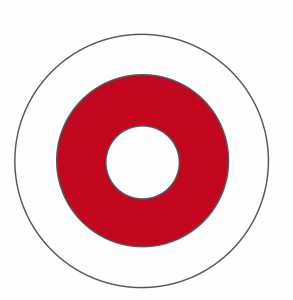
3: Tactical Threat Intelligence
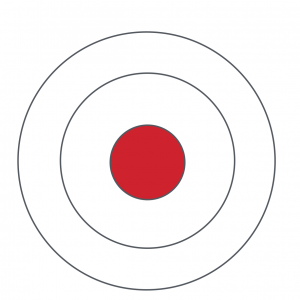
Building an Effective Threat Intelligence Program
A properly implemented threat intelligence program is one that is built to specifically address the organization it serves. Below are five guidelines security teams should consider as they implement their program.
1: Consider the organization’s threat profile and like adversaries.
Tune selected intel sources to match your expected threat actors. It can’t hurt to evaluate a wide range of intel sources, but these should be carefully evaluated in the light of the organization’s needs before activating. For example, a financial organization would not have much use for intelligence about threat groups that primarily steal medical records.
2: Integrate to the instrumentation within the environment.
This may include a technical integration to the SIEM, or simply ensuring the team can search available evidence for the specific types intelligence indicators (IP address, hostname, traffic signatures, etc.) Related to this point, consider the longevity for an item of threat intelligence and whether the organization’s data retention policies match the expected use case.
3: Continuously evaluate effectiveness.
Is a particular intel indicator creating an excessive number of false positive events? That may require re-evaluating the indicator or potentially the entire intelligence source. The indicator may require fine tuning or modification to best suit its intended purpose.
4: Remove when no longer useful to the operations process.
In the case of an indicator that is no longer useful, it should be removed. There is rarely value to alerting on tactical intelligence from several years ago. This is closely related to the re-evaluating point above, but many organizations fail to implement cleanup processes. Doing so minimizes the chance of false positives, but also ensures real-time detection platforms are seeking out only the most valuable events.
5: Generate internal intelligence as a result of DFIR processes.
Solely consuming threat intelligence is not enough to create a viable threat intel program. Operations teams behind the most effective programs include an input from the DFIR processes through which locally-generated threat intel is consumed. As the DFIR teams learn more about an attacker or campaign, context is added and those indicators become intelligence. By establishing a feedback loop to security operations, the threat intel can yield quick and specific detections.
Key Takeaways
The points above still barely scratch the surface of what is needed to integrate a threat intelligence component to an existing information security program. However, it is clear that simply “buying an intel feed” is a woefully inadequate approach. In fact, it may be worse than deferring the idea of threat intelligence entirely. If poorly implemented, it could result in countless false positives (wasting personnel time chasing nonexistent threats) or give the organization a false sense of security despite an expensive subscription fee.
All of this points to the clear fact that threat intelligence is a complex facet to an overall information security program. As seen countless times throughout the brief history of this industry, there are no easy solutions to the complex problems delivered by dedicated and resourceful human attackers. Threat Intelligence is often one of the last implemented programs for many organizations because it requires a sound operational and investigative foundation on which it can be built. A threat intelligence program is a continuous process, and requires both human and technical investments to be successful.